Introducing AI-Assisted Incident Response

Harness the speed and capability of AI without losing control. Valhuntir forces human-in-the-loop controls to ensure investigative decisions and conclusions remain with the human examiner.
Digital forensics and incident response began with low-level tools such as dd and hex editors. Over time the tooling became more complex, automating many of the tasks that the examiner previously did by hand. Artificial intelligence is the latest extension of this automation. But the human examiner must assess the evidence, determine its meaning in the context of the incident, and let the evidence inform the next steps of the investigation.
Left to its own devices, artificial intelligence can hallucinate, misinterpret, and reach erroneous conclusions.
The human examiner's guidance throughout the entire investigative process remains essential for reviewing each critical finding and ultimately being responsible for those conclusions. Nonetheless, artificial intelligence can streamline many investigative steps, conduct useful research, correlate large datasets, and significantly improve the efficiency of the investigative process.
AI technologies are undergoing constant change, and the pace of that change is only going to increase.
Rather than try to maintain continuous updates on the ever-shifting state of this art, we have decided to release our thoughts in code. The platform serves as our current commentary on how best to manage the interaction between artificial intelligence and human examiners.
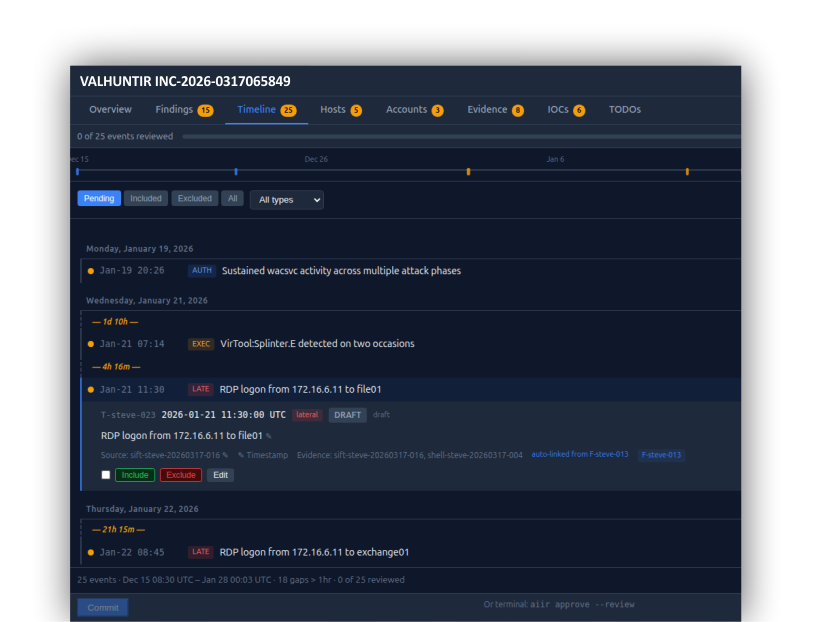
VALHUNTIR
AI Incident Response platform with varying levels of human-in-the-loop review and control based on your deployment needs. CLI and architecture reference.
In its simplest form, Valhuntir provides Claude Code with forensic knowledge and instructions on how to enforce forensic rigor, present findings for human review, and audit actions taken. MCP servers enhance accuracy by providing authoritative information — a forensic knowledge RAG and a Windows triage database — plus optional OpenCTI threat intelligence and REMnux malware analysis.
SIFT MCP
Monorepo for all SIFT-side Valhuntir components. 11 packages: forensic-mcp (12 tools + 14 resources), case-mcp (14 tools), report-mcp (6 tools), sift-mcp (6 tools), sift-gateway, forensic-knowledge, forensic-rag, windows-triage, opencti, sift-common, and case-dashboard. Part of the Valhuntir platform.
Windows Tools MCP
Catalog-gated Windows forensic tool execution with knowledge-enriched response envelopes.
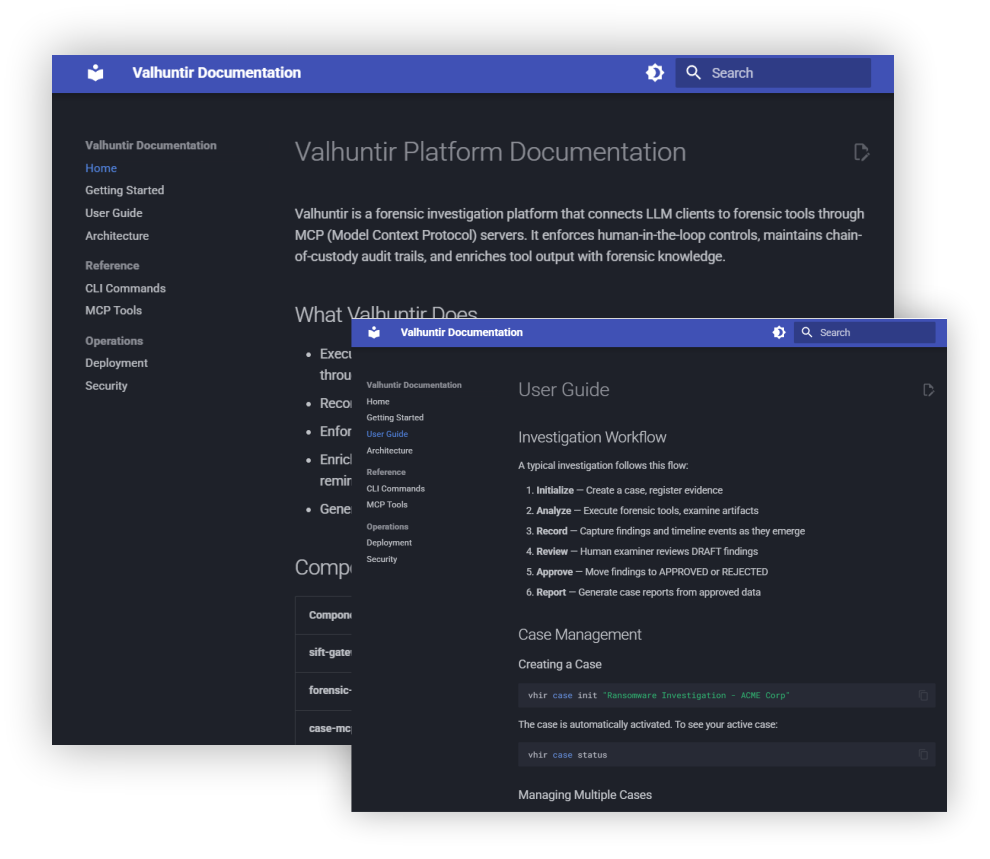
Valhuntir Platform Documentation
Valhuntir is a forensic investigation platform that connects LLM clients to forensic tools through MCP (Model Context Protocol) servers. It enforces human-in-the-loop controls, maintains chain-of-custody audit trails, and enriches tool output with forensic knowledge.
What Valhuntir Does
- Executes forensic tools (Zimmerman suite, Volatility, Sleuth Kit, Hayabusa, and more) through catalog-gated MCP servers
- Records findings, timeline events, and investigation reasoning with full audit trails
- Enforces human approval for all findings before they enter reports
- Enriches tool output with artifact caveats, corroboration suggestions, and discipline reminders from forensic-knowledge
- Generates IR reports using data-driven profiles with Zeltser IR Writing guidance
MAKE YOUR TOUGH JOB EASIER WITH THE FREE RESOURCES WE PROVIDE
LATERAL MOVEMENT ANALYSIS / EVENT LOG ANALYSIS / MEMORY ANALYSIS AND MORE